Monti Ransomware Sold! New Owners Hint Future Plans

The change in ownership and a shift in focus towards Western countries highlights a new approach towards ransomware.
Ashish Khaitan June 12th, 2024

Share on LinkedInShare on Twitter
The notorious Monti ransomware has been sold to new owners. According to the actor’s latest update, “This project was bought. It was bought because it suited our goals perfectly and did not have a bad reputation.”
The change in ownership and a shift in focus towards Western countries highlights a new approach towards ransomware. According to recent statements, the project has been acquired, with new owners expressing their intentions to revamp its infrastructure for future endeavors.
In a cryptic post on their platform, the group hinted at upcoming developments, rallying for a collaborative effort to “build the future of the USA and Europe together.”
Monti Ransomware Group and Change in Ownership
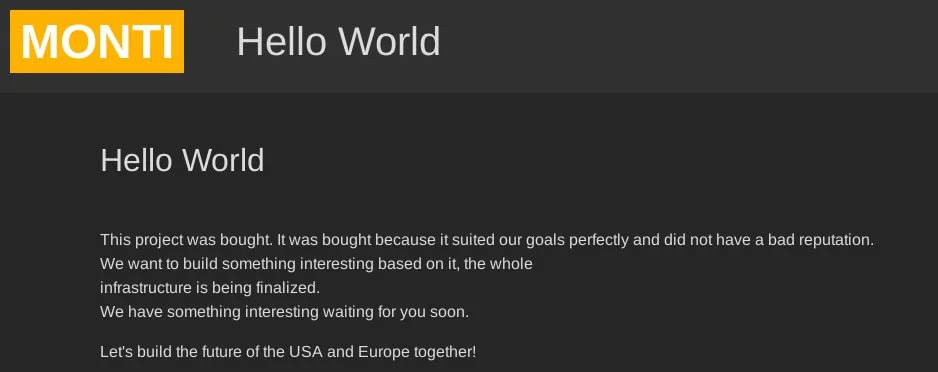
Source: Dark Web
This announcement follows a string of cyberattacks perpetrated by the Monti ransomware gang. Notably, a recent incident in the South of France targeted three prominent institutions simultaneously: the Pau-Pyrénées airport, the Pau business school, and the city’s digital campus. These attacks, occurring overnight from May 12 to May 13, 2024, disrupted operations and raised concerns regarding cybersecurity vulnerabilities in critical sectors.
While the affected institutions scrambled to mitigate the fallout, journalists uncovered insights from the Chamber of Commerce and Industry (CCI) shedding light on the situation. Despite assurances of minimal disruption to activities, the compromised digital infrastructure left a trail of compromised data, including sensitive documents and personal information of employees and students.
The modus operandi of the Monti ransomware group draws parallels to its predecessors, notably the Conti ransomware, which ceased operations in May 2022. The emergence of Monti, with its similar tactics and techniques, suggests a strategic emulation aimed at exploiting the void left by Conti’s absence.
A Deeper Dive into Monti Ransomware Group
A deeper dive into the Monti ransomware incident reveals a sophisticated operation orchestrated through the exploitation of vulnerabilities like the notorious Log4Shell. The attackers infiltrated networks, encrypted user desktops, and disrupted critical server clusters, leaving organizations grappling with the aftermath.
Despite its relative obscurity, the Monti ransomware group has garnered attention within the cybersecurity community. Analysts speculate that the group’s emulation of Conti’s strategies may stem from the leaked trove of Conti’s internal data, providing a blueprint for nefarious activities.
As cybersecurity threats evolve, it becomes imperative for organizations to fortify their defenses and stay vigilant against threat actors like the Monti ransomware. Collaborative efforts between cybersecurity experts and stakeholders are essential to mitigate risks and safeguard critical infrastructures from malicious actors.