Kraken Vs Certik: A Dispute Over $3 Million 0-Day Bug Bounty

While Kraken is treating this as a criminal case, CertiK urged them to cease any threats against their white hat hackers.
Mihir Bagwe June 20th, 2024

Share on LinkedInShare on Twitter
In a high-stakes clash within the crypto verse, Kraken, a leading U.S. cryptocurrency exchange, has accused blockchain security firm Certik of illicitly siphoning $3 million from its treasury and attempting extortion.
The dispute shows the significant tensions between ethical hacking practices and corporate responses and underscores the complexities and challenges within the bug bounty ecosystem.
Accusations from Kraken
Nick Percoco, Kraken’s chief security officer, took to social media platform X (formerly known as Twitter) to accuse an unnamed security research firm of misconduct. According to Percoco, the firm – later revealed to be Certik – breached Kraken’s bug bounty program rules.
Instead of adhering to the established protocol of promptly returning extracted funds and fully disclosing bug transaction details, Certik allegedly withheld the $3 million and sought additional compensation, Percoco claimed.
Percoco claimed that “the ‘security researcher’ disclosed this bug to two other individuals who they work with who fraudulently generated much larger sums. They ultimately withdrew nearly $3 million from their Kraken accounts. This was from Kraken’s treasuries, not other client assets.”
He said that after contacting the researchers, instead of returning the funds they “demanded a call with their business development team (i.e. their sales reps) and have not agreed to return any funds until we provide a speculated $ amount that this bug could have caused if they had not disclosed it. This is not white-hat hacking, it is extortion!”
Percoco said that in the decade-long history of Kraken’s bug bounty program, the company had never encountered researchers who refused to follow the rules. The program stipulates that any funds extracted during bug identification must be immediately returned and accompanied by a proof of concept. The researchers are also expected to avoid excessive exploitation of identified bugs.
The dispute escalated as Certik reportedly failed to return the funds and accused Kraken of being “unreasonable” and unprofessional. Percoco responded that such actions by security researchers revoke their “license to hack” and classify them as criminals.
“As a security researcher, your license to “hack” a company is enabled by following the simple rules of the bug bounty program you are participating in. Ignoring those rules and extorting the company revokes your “license to hack”. It makes you, and your company, criminals.”
Certik’s Response to Kraken
Following Kraken’s public accusations, Certik disclosed its involvement and countered Kraken’s narrative by accusing the exchange of making unreasonable demands and threatening its employees. Certik claimed Kraken demanded the return of a “mismatched” amount of cryptocurrency within an unfeasible timeframe without providing necessary repayment addresses. The company provided an accounting of its test transactions to support its claims.
Certik shared its intent to transfer the funds to an account accessible to Kraken despite the complications in the requested amount and lack of repayment addresses.
“Since Kraken has not provided repayment addresses and the requested amount was mismatched, we are transferring the funds based on our records to an account that Kraken will be able to access.” – CertiK
CertiK’s Take on Kraken’s Defense Systems
Certik defended its actions and instead highlighted the inadequacy of Kraken’s defense systems. The firm pointed out that the continuous large withdrawals from different testing accounts, which were part of their testing process, should have been detected by Kraken’s security measures. Certik questioned why Kraken’s purportedly robust defense systems failed to identify such significant anomalies.
“According to our testing result: The Kraken exchange failed all these tests, indicating that Kraken’s defense in-depth-system is compromised on multiple fronts. Millions of dollars can be deposited to ANY Kraken account. A huge amount of fabricated crypto (worth more than 1M+ USD) can be withdrawn from the account and converted into valid cryptos. Worse yet, no alerts were triggered during the multi-day testing period. Kraken only responded and locked the test accounts days after we officially reported the incident.” – CertiK
The blockchain security firm said the fact behind their white hat operation is that “millions dollars of crypto were minted out of air, and no real Kraken user’s assets were directly involved” in these research activities.
The firm also said that the dispute with the cryptocurrency exchange is actually shifting focus away from a more severe security issue at Kraken.
“For several days, with many fabricated tokens generated and withdrawn to valid cryptos, no risk control or prevention mechanisms were triggered until reported by CertiK,” it said. “The real question should be why Kraken’s in-depth defense system failed to detect so many test transactions.”
Regarding the money siphoned, Certik said, “Continuous large withdrawals from different testing accounts was a part of our testing.” With an aim of transparency, the security firm disclosed details of all testing deposit transactions and the timeline of how the bug bounty saga played out on X.
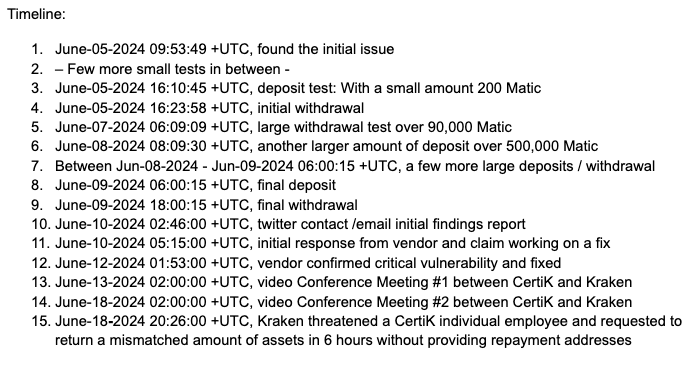
Timeline of the Kraken vs CertiK zero-day and bug bounty dispute (Source: CertiK on platform X)
Disclosure of Product Flaws Treads a Fine Line
The news of the escalated dispute comes on the heels of another incident where a white hat hacker – after following bug bounty ethics – was threatened by the legal team of the company to “cease and desist.”
Andrew Lemon, an offensive security expert, responsibly reported a critical vulnerability to an unnamed company that manufactured and sold a traffic control system. The vulnerability allowed a remote unauthenticated attacker to bypass security and gain full control of a traffic controller, giving them the ability to changing stoplights and modify traffic flow, Lemon explained in a LinkedIn post.
But to Lemon’s surprise, instead of acknowledging and addressing the bug with the engineering team, its legal team threatened to sue him under the Computer Fraud and Abuse Act.
“I Received a letter from a company’s legal team instead of engineering after responsibly disclosing a critical vulnerability in a traffic control system I purchased from eBay,” he said.
“The company’s response? In order for them to acknowledge the vulnerability, hardware must be purchased directly from them or tested with explicit authorization from one of their customers, they threatened prosecution under the Computer Fraud and Abuse Act, and labeled disclosure as irresponsible, potentially causing more harm.”
Security Engineer Jake Brodsky responded saying, “Legally they’re not wrong for writing such a letter or even bringing a court case against the researcher. However, ethically, because it pits professional organizations against each other for no good reason, it is problematic.”
Disclosure of product flaws treads a very fine line. On the one hand, nobody likes the publicity that follows. On the other hand, if nobody says anything, the only way we can improve is in the aftermath of an investigation where fortunes are lost and people get hurt.
Implications for the Bug Bounty Ecosystem
The Kraken-Certik dispute and the one highlighted by Andrew Lemon raises critical questions about the operational dynamics and ethical boundaries within bug bounty programs. These programs are designed to incentivize security researchers to identify and report vulnerabilities, offering financial rewards for their efforts. However, these cases reveal potential pitfalls when communication and mutual understanding between parties break down.
The ethical framework of bug bounty programs relies on clear rules and mutual trust. Researchers must adhere to the program’s guidelines, including the immediate return of any extracted funds and full disclosure of their findings. On the other hand, companies must provide clear instructions and maintain professional interactions with researchers.
There is a need for well-defined protocols and communication channels between companies and researchers. Ensuring transparency and clarity in expectations can prevent misunderstandings and conflicts, fostering a more cooperative environment for cybersecurity improvements.





